What Makes Portmaster A Great Alternative to Pi-hole
Both Portmaster and Pi-hole are free and open source privacy tools. The Portmaster has an easy set up with great privacy defaults, giving you a simple way to fully control your device, wherever you go. The Pi-hole on the other hand needs some initial setup; but for the skilled it is a capable tool for managing your home network.
Overview Chart
| Portmaster | Pi-hole | |
|---|---|---|
| Open Source | ||
| Setup | Easy | Advanced |
| Protection Type | Device | Network |
| Availabilty |
|
|
| Secure DNS | ||
| Individual Apps Settings | ||
| Adaptive Threat Model |
Detailed Comparison
One Shoe Does Not Fit All - What Is Your Threat Model?
What is the best way to protect diamonds worth a few thousand dollars?
You could leave them in your living room for everyone to see.
But that would be careless.
You could build an atomic bomb shelter in the middle of the woods.
But that would overdo it.
A safe in your house is probably a better solution.
Welcome to the world of threat modeling. Before choosing any tool, especially within privacy, it is important to ask
- What do I want to protect?
- From whom do I want protection?
- How much time can I invest?
We need different solutions for different needs - there simply is no perfect solution for everyone. You are the only one who knows the value of your diamonds and who is after them. So only you can decide which solution is best for you.
Understanding your threat model might be difficult at first, but it will save you a lot of time and help you avoiding wrong decisions. This comparison blog showcases the strengths and weaknesses of the Portmaster and the Pi-hole and hopes to assist you in your decision making.
Portmaster and Pi-hole Are Free and Open Source
An auditable and open source code builds a high level of trust in the software. Instead of having to trust a privacy policy of the company, people can check the source code and see what it really does on a technical level.
The beauty with this is, the bigger the community around a software gets, the more secure it becomes, often outperforming proprietary software. Zero-day exploits and long-forgotten vulnerabilities become rarer since someone from the community usually discovers them.
The Portmaster and Pi-hole are both free and open source, with great communities involved. They are also both transparent about their funding which gives additional insight into their organization and motives. (Portmaster / Pi-hole)
Portmaster Is Beginner Friendly
Protecting your privacy should not require a high level of technical expertise, which is why the Portmaster is designed to be simple for beginners. It is easy to setup and the default settings improve your privacy right out of the box.
However, experts can spend hours upon hours to configure every aspect to their needs, as mentioned in later passages.
Portmaster Protects Your Device, Pi-hole Your Network
The Pi-hole’s scope of protection is very different from the Portmaster’s. Since the Portmaster is an on-device network blocker, it will stop unwanted connections from leaving your computer even before the DNS.
The Pi-hole on the other hand will act as a DNS server, allowing many devices to connect to it and filtering traffic for all those devices. The Pi-hole can be used on the client-side with some additional setup, but because of its technical architecture, it is best used as a network service.
In comparison to the Portmaster, Pi-hole often involves the usage of extra hardware, such as a Raspberry Pi or a Virtual Private Server (VPS) as the server. This could result in additional costs and maintenance.
More setup and technical knowledge is required to access it outside the local network and keep the server secure. In the end, it may well be worth the extra efforts if your threat model demands it.
The documentation for the Pi-hole and Portmaster will provide more details if you wish to dig into the technical details.
Portmaster Allows You to Configure Settings System-Wide and Per-App
The Portmaster has global settings which define behavior for the whole device. But sometimes, an application may break due to a blocked connection. Allowing that connection system-wide might hurt your privacy. With the Portmaster, you can easily solve this problem by creating an exception for a specific application, leaving other apps unaffected.
You can even block risky connection types system-wide, such as p2p or incoming, and then create exceptions for trusted apps.
Pi-hole Can Manage All Your Devices
Many aspects of the Pi-hole are comparable to those of the Portmaster, such as content blocking, filter lists, query logs, etc. However, since the Pi-hole is a server it also has advantages over the Portmaster. It can be used to secure your whole local network, as well as any other device that can connect to the Pi-hole over the Internet.
Smart TVs, smart devices and printers in your network may send telemetry data or display advertisements. In such situations a Pi-hole is well suited, as many hardware and software limitations prevent the installation of client-side blockers like the Portmaster. The Pi-hole will prevent advertisements, trackers, and other intrusions at the network DNS level.
Any changes you make to the Pi-hole settings will be applied to all devices that use it to route their connections. It is not possible to change and save settings for a device or app individually.
Additional capabilities of the Pi-hole includes Gravity script, the Pi-hole command, Telnet API, customized logs and DHCP management, all of which will help you better manage your devices.
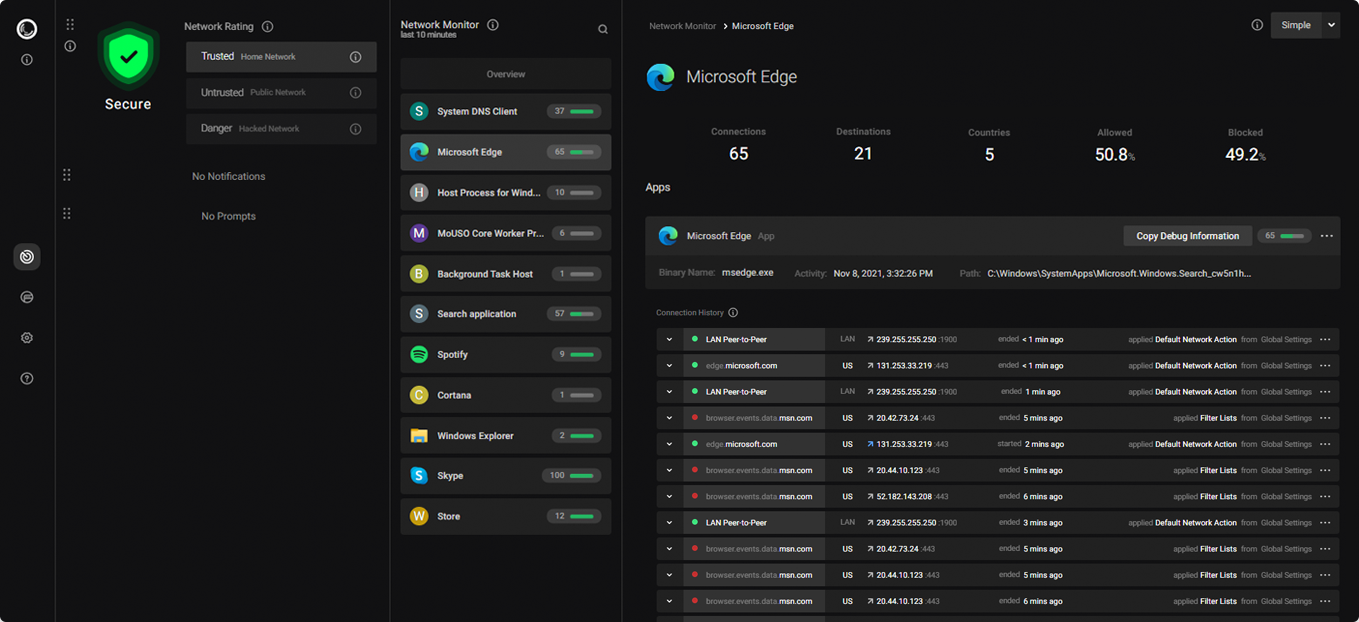
Portmaster and Pi-hole Both Provide a Simple Dashboard for Detecting and Responding to Privacy Threats
The interfaces of Portmaster and Pi-hole are both sleek and provide a pleasant user experience. Because of the significant technical variations between them, they have quite the distinct tweaking possibilities: The Pi-hole can display metrics from all devices on the network and can prevent devices from accessing the Internet at the network DNS level.
The Portmaster enables you to see connections made from specific apps on your device. This allows you to fully block Internet access for individual applications or block specific, unwanted connections. For even stricter settings, you can block Internet access on the device level and then create individual exceptions for applications.
Both Safeguard Your DNS queries From ISPs to Enhance Your Privacy
The Pi-hole needs some setup to encrypt DNS queries, while the Portmaster does this by default. With encrypted DNS, your DNS provider is the only one who can keep track of your DNS requests while Internet Service Providers (ISPs) and eavesdroppers can no longer easily determine the websites you browse or the apps you use. You also enjoy enhanced security by preventing threats like DNS based man-in-the-middle (MITM) attacks.
Even if your ISP is uninformed of the websites you visit, they can monitor the IP addresses you connect to. Since many services employ dedicated static IPs for their infrastructure, ISPs can still track your queries using conditional logic. So even though DNS encryption improves your privacy, it cannot safeguard all your connections.
We recommend using Tor, a trusted VPN or the SPN (Portmaster Add-On), which will provide additional privacy from your ISP.
The Portmaster Adapts to Your Threat Model
Different places have different threats. Your home network is more trustworthy than a WiFi at a coffee shop.
With the Portmaster, you can configure settings to be active in one situation but not in the other, like allowing sensitive connections at home but not at the public library.
This enables you to configure settings for different situations: as soon as your situation changes, all you need to do is flip a switch and all settings will immediately adapt to your configured threat model.
Portmaster also has a Simple/Advanced switch that shows or hides settings, allowing you to get even more control over your threat model.
Both Solutions Can Be Used Alongside an Existing VPN Connection
The Portmaster and the Pi-hole support running alongside a VPN. Some VPNs require additional setup, so it is always good if you check the compatibility of your VPN in the latest docs of the Portmaster and the Pi-hole.
Portmaster Makes It Easy to Block Domains By Category
The Portmaster allows you to easily block ads, trackers, malware and NSFW sites via integrated domain filter lists. You can manage these lists for your full device or configure them for individual applications.
These lists are created and maintained by privacy and security communities and are also used by browser extensions, the Pi-hole, etc.
Additionally, you can block all subdomains of entries in selected filter lists to further tighten your privacy.
Conclusion
We Recommend: Start With Portmaster; Use the Pi-hole When Managing Your Home Network
Both the Portmaster and Pi-hole are open source solutions which greatly improve your privacy. The Portmaster is easily set up and has great privacy defaults. This gives you a simple way to fully control your device, wherever you go. The Pi-hole on the other hand needs some initial setup; but for the skilled it is a great tool for controlling and managing your home network.
December 9, 2021 • Written by Safing
Updated: April 22, 2026 • Updated by Viktor